Restricting Access to EC2 Instances Based on Tags
The principle of least privilege is key when it comes to securing your infrastructure on AWS. For example, an engineer should only be able to control EC2 instances that are in scope for her day-to-day work. But how do you make sure an engineer is only allowed to …
- start, stop, and terminate specific instance?
- create, attach and delete specific volumes?
- create, restore and delete specific snapshots?
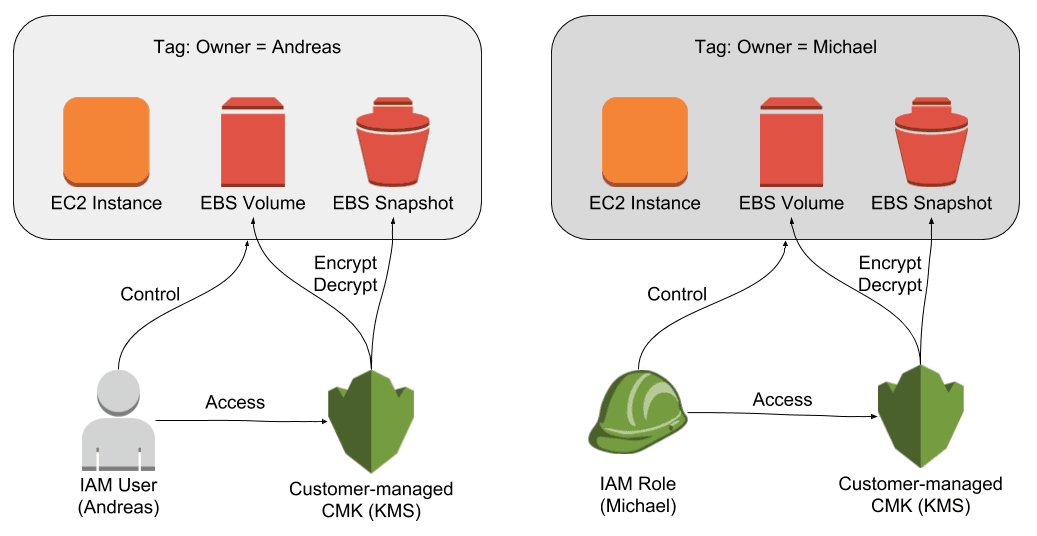
As illustrated in the following figure you can restrict access to EC2 instances, EBS volumes, and EBS snapshots by making use of …
- tags attached to EC2 instances, EBS volumes, and EBS snapshots.
- an IAM role or user to authenticate an engineer.
- an IAM policy restricting access to the EC2 instances, EBS volumes, and EBS snapshots based on tags.
- a customer-managed CMK (KMS) to encrypt and decrypt data stored on EBS volumes and snapshots.
Attach the following IAM policy to a user or role to restrict access to instances, volumes, and snapshots based on a tag.
Replace <TAG_KEY> with the key you want to use for the tag (e.g. owner). Replace <TAG_VALUE> with an identifier of the user or role (e.g. andreas). Replace <KMS_KEY_ARN> with the ARN of the customer-managed CMK which only the user or role is allowed to use.
** Note: I’ve added # comments to the IAM policy to explain the details. Please remove all # comments before making use of the policy. The JSON is not valid otherwise.**
{ |
As the IAM policy references a tag and a customer-managed CMK, it is necessary to use a separate policy per user or role.
Please note, AWS extended the IAM conditions for EC2 heavily during the past months and years. The following information is no longer correct.
Why do we need to use a customer-managed CMK? Because it is not possible to restrict who can restore an EBS snapshot by using tags. Therefore, any engineer could access the data stored on any snapshot. Encrypting all volumes and snapshots with a customer-managed CMK (KMS) is a workaround allowing you to control very fine-granular which engineers can access data stored on volumes and snapshots.
It is also important to note, that it is not all action support conditions by tags. For example, it is not possible to restrict engineers from attaching a networking interface (ec2:AttachNetworkInterface) to any of the instances. If you want to be able to isolate your resources without any limitations, choose a multi-account strategy instead.
For details about IAM policies for EC2 go to the official AWS Documentation.
Further reading
- Article Cleaning up an S3 bucket with the help of Athena
- Article AWS Security Primer
- Article Event Driven Security Automation on AWS
- Tag security
- Tag iam
- Tag kms
